PRIVACY
PROTOCOL.
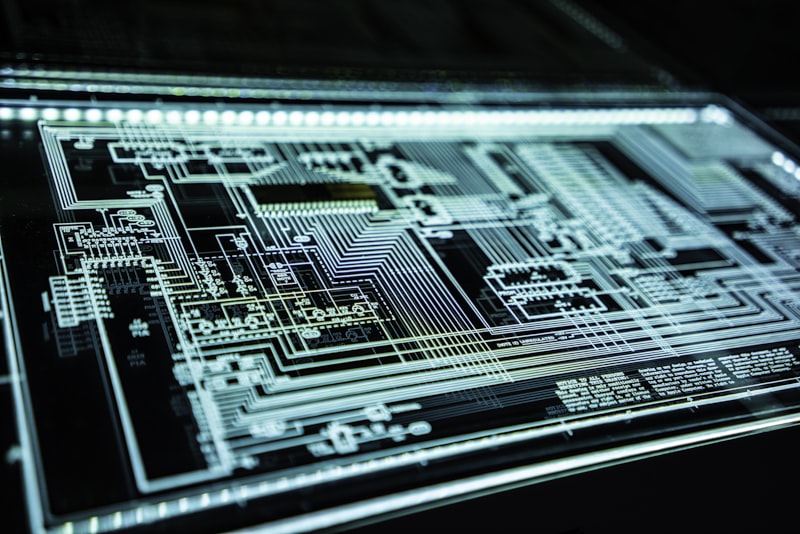
Secure Node Encryption // Version 4.0 // PropReach Matrix
ISO 27001 Data
Integrity & Hashing
PropReach infrastructure is engineered on the premise of zero-trust architecture. Every data packet entering our RCS engine undergoes a multi-layer SHA-512 hashing process before being routed to the DLT clearance nodes.
Data Acquisition & Indexing
We ingest campaign metadata including sender credentials and target lists. This data is logically isolated into encrypted shards that exist only for the duration of the campaign lifecycle.
HNI data is scrubbed and never stored in plain-text format across any PropReach nodes.
DLT & TRAI Legal Clearance
In total compliance with Indian TRAI regulations, our matrix interfaces directly with the DLT framework. We act as a service provider hub that enforces content scrubbing against approved templates.
Unauthorized template modifications are auto-flagged and terminated by the system watchdog.
Signal Surveillance & Analytics
Delivery receipts and interaction telemetry are monitored to provide real-time ROI maps. These metrics are anonymized and stored on a 30-day rotation cycle.
Surveillance logs are end-to-end encrypted and accessible only via biometric API keys.
Matrix Cryptography Standards
We employ asymmetric RSA-4096 key exchanges for all client-to-server communications. This ensures that even if a node is compromised, the data within remains unreadable without the matrix-origin key.
Key rotations occur every 24 hours to ensure perpetual signal secrecy.
Retention & Permanent Erasure
Data Sovereignty is our core principle. Upon campaign termination or client request, we execute a 'Deep Wipe' protocol—overwriting the allocated storage blocks with random noise seven times.
Physical server drives are decommissioned and destroyed in specialized ISO facilities.
Cross-Border Node Governance
While our core nodes are optimized for pan-India delivery, backup nodes comply with global GDPR and CCPA standards, ensuring a universal baseline of privacy regardless of signal origin.
Data remains within the Indian Territory for all domestic DLT-regulated campaigns.
User Sovereignty
Your Rights within
the Matrix
- Right to immediate node isolation
- Access to real-time encryption logs
- Data portability via encrypted JSON payloads
- Automatic DLT registration withdrawal
"Privacy is not a feature; it is the fundamental system architecture upon which PropReach/InfozySMS is validated. We do not negotiate on data integrity."
Request an Audit.
Verified real estate partners can request a complete system audit and penetration testing summary for their dedicated campaign nodes.
